Tech Blog
Custom software, AI, cloud architecture, cybersecurity and mobile development — written by the w//b studio team.
10 articles published

Agentic AI: What It Really Means for Your Business (And Why Security Changes Everything)
Agentic AI is no longer a concept for the future — it's reshaping how businesses operate today, enabling autonomous systems that plan, decide, and act without constant human input. But with this new power comes a critical question: how do you keep these systems secure, controlled, and aligned with your business goals? Understanding both the opportunity and the risk is the key to deploying Agentic AI responsibly.

NIS2 vs ISO 27001: Key Differences and What Your Business Really Needs
NIS2 and ISO 27001 are two of the most important cybersecurity frameworks businesses face today, but they serve different purposes and carry different obligations. Understanding the distinction between a legal directive and a voluntary standard can save your organization time, money, and compliance headaches. This article breaks down both frameworks and helps you decide which one—or both—your company needs.
Vibe Coding: Revolution or Trap? What No AI Vendor Tells You About Building Software Without Developers
Vibe coding promises anyone can build software using AI—no developers needed. But behind the hype lies a set of hidden risks, technical debt, and limitations that AI vendors conveniently leave out. This article breaks down the real cost of going codeless with AI and what you need to know before betting your product on it.

Transform Your Business with AI: How w//b studio tech Accelerates Innovation and Cuts Costs
Artificial intelligence is no longer a luxury reserved for tech giants — it's a practical tool any business can leverage today. w//b studio tech helps companies integrate AI solutions that streamline operations, reduce overhead, and unlock new growth opportunities. Discover how a smart AI strategy can give your business a measurable competitive edge.

Operation PowerOFF Took Down 53 DDoS Domains — Here Is What Your Business Should Learn From It
International law enforcement dismantled 53 DDoS-for-hire domains in Operation PowerOFF, striking a major blow against cybercriminals. This coordinated takedown exposes how accessible DDoS attacks have become and why businesses can no longer afford to ignore the threat. Here's what every organization should take away from this landmark operation.

GDPR Compliance Checklist for SaaS Platforms in 2026: What's Changed and What Still Trips Companies Up
GDPR compliance remains one of the most complex challenges for SaaS companies, and 2026 has brought fresh regulatory updates that many platforms are still scrambling to address. This checklist covers the latest requirements, common pitfalls, and practical steps to keep your SaaS business compliant. Whether you're a startup or scaling enterprise, staying ahead of GDPR is non-negotiable.

Russia's Router Hijacking Campaign to Steal Microsoft Office Tokens: 5 Immediate Steps for European Businesses
Russian state-sponsored hackers are actively compromising routers to intercept Microsoft Office 365 authentication tokens, putting European businesses at severe risk. This attack bypasses traditional security measures by targeting network infrastructure rather than endpoints. Discover five immediate steps your organization can take to defend against this sophisticated threat.

How to Use AI to Automate Cyber Threat Monitoring Without a Large Security Team
Most small and mid-sized companies can't afford a full security operations center, but AI-powered tools are changing the game. This guide explains how to leverage artificial intelligence to detect, analyze, and respond to cyber threats automatically. You'll learn which tools to use, how to set them up, and what to watch out for.
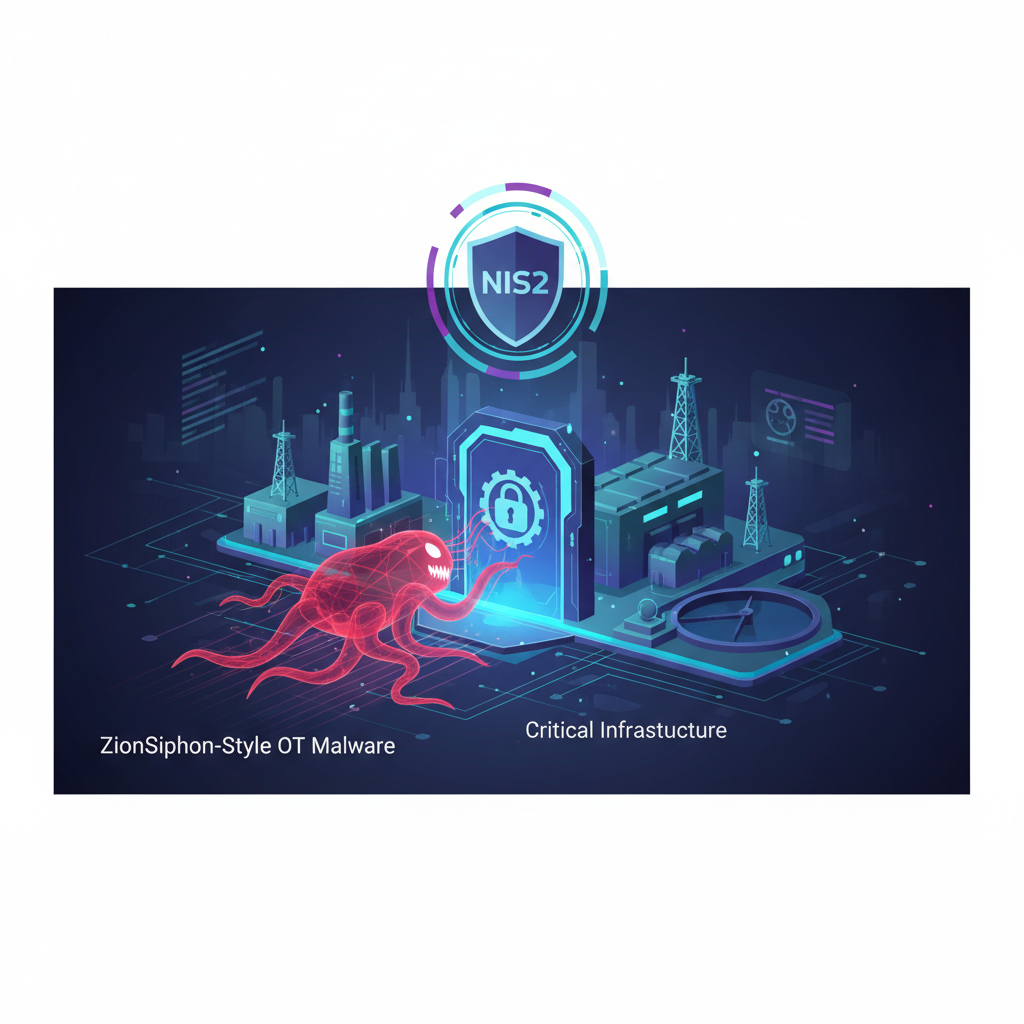
NIS2 and Critical Infrastructure: What ZionSiphon-Style OT Malware Means for Your Compliance Obligations
As OT-targeting malware like ZionSiphon grows more sophisticated, critical infrastructure operators face mounting pressure to align cybersecurity defenses with NIS2 compliance requirements. Understanding how these threats exploit industrial control systems is essential for risk management and regulatory adherence. This article breaks down what NIS2 demands and how to close the gaps before an attack exposes your vulnerabilities.

AI-Powered Vishing Attacks Are Here: How to Train Your Employees to Recognize Them
AI-powered vishing attacks use cloned voices and deepfake audio to deceive employees into revealing sensitive information or transferring funds. These threats are more convincing than ever, making traditional security awareness training insufficient. Learn how to equip your team with the skills to detect and stop these sophisticated voice-based scams.
